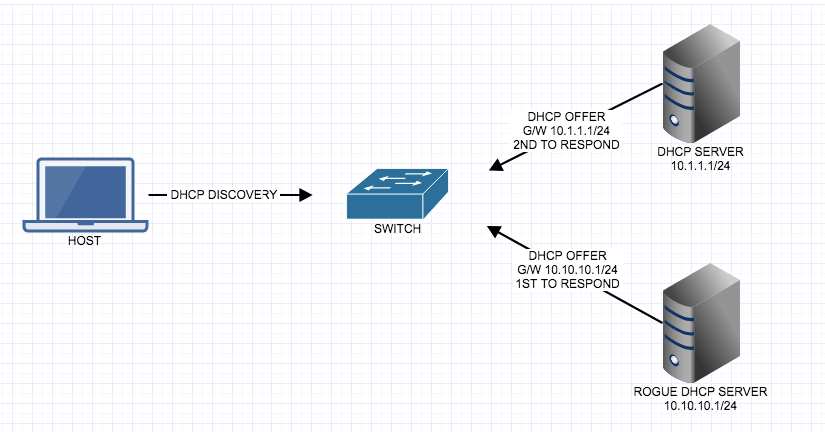
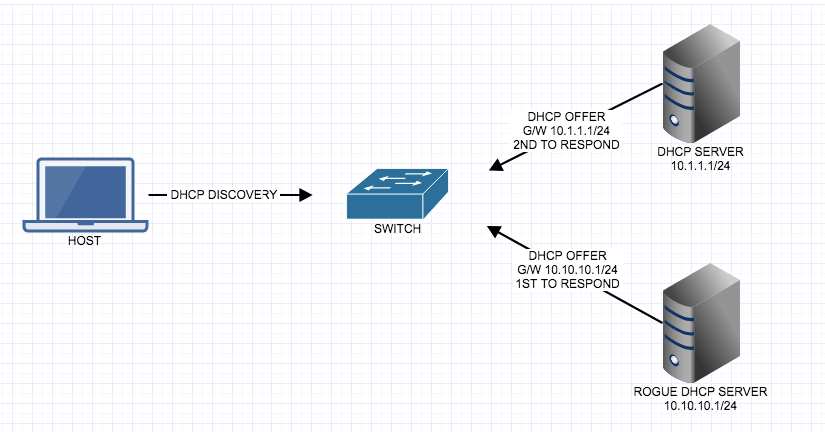
DHCP seems like a seemingly innocent, but common protocol, that can be used against our network. Since we know the DHCP discovery packet is a broadcast packet, just looking for a DHCP server and the host doesn’t care what DHCP server sends a DHCP OFFER back, it will accept the first offer, the DHCP offer includes information such as IP address, Subnet Mask, Default Gateway, DNS information. What if the first offer that is returned is a Rouge or Malicious DHCP server? Does that mean all traffic from that host using the Rogue DHCP servers gateway could be looking at all of the traffic passing through it? Yes! We can prevent this from happening with a feature called DHCP Snooping.
DHCP Snooping is going to snoop or listen into DHCP traffic to make sure that DHCP conversations go to the correct interface and allow that traffic to pass, otherwise it will be dropped. The interfaces to a known good DHCP server will be ‘trusted’ and all other interfaces will be untrusted, therefor the switch will know if DHCP conversations are happening on an untrusted interface then the traffic will be dropped and the interface will be put into err-disabled mode.
By default the switch considers all ports untrusted. We have to enable DHCP snooping globally, then trust at the interface level. IP ARP inspection and IP source-guard are dependent on DHCP snooping being enabled.
Enabled DHCP Snooping
tpw-sw1(config)#ip dhcp snooping
Enable DHCP Snooping on a VLAN
tpw-sw1(config)#ip dhcp snooping vlan 10
Trust Interface with DHCP server on it
tpw-sw1(config)#int gigabitEthernet 1/1
tpw-sw1(config-if)#ip dhcp snooping ?
information DHCP Snooping information
limit DHCP Snooping limit
trust DHCP Snooping trust config
tpw-sw1(config-if)#ip dhcp snooping trust
DHCP option 82
When packets come in on an untrusted port with option 82 set, those packets are not dropped. The switch will insert its own DHCP option 82 information (the switches MAC address), and when the packet is returned it will make sure its own DHCP option 82 information is in the reply if it is, it will remove its option 82 information and forward the packet normally, if not it will drop it. This check is enabled by default.
Turn off the validity check
tpw-sw1(config)#no ip dhcp relay information check
Turn on Option 82
tpw-sw1(config)#ip dhcp snooping information option
Show Commands
tpw-sw1#sh ip dhcp snooping
Switch DHCP snooping is enabled
DHCP snooping is configured on following VLANs:
10
DHCP snooping is operational on following VLANs:
10
DHCP snooping is configured on the following L3 Interfaces:
Insertion of option 82 is enabled
Option 82 on untrusted port is not allowed
Verification of hwaddr field is enabled
Verification of giaddr field is enabled
DHCP snooping trust/rate is configured on the following Interfaces:
Interface Trusted Relay Info policy Rate limit (pps)
------------------------ ------- ----------------- ----------------
GigabitEthernet1/1 yes unlimited