Telnet is a Network protocol that allows users to connect to and administer a devices Command Line Interface (CLI). However all of the information exchanged on a Telnet session is unencrypted, this means is someone is sniffing the traffic from your host to the device it can be read clearly. So now all know telnet is a super un-secure way to access the CLI of a device, and you should always use SSH where you can, but Telnet can be used in another way. Telnet can only be used to verify network connectivity to remote devices that are TCP based, because TCP is a connection-oriented protocol.
I get requests all the time to open up specific ports on the firewall. You can find a list of the well know port numbers here.
Before I start poking holes in the firewall or other device I check to see if it is already open.
Telnet will by default only check and listen on TCP port 23
If a user asks me is https (port 443) is open to and on a specific server you can easily test with Telnet.
You simply add the port number at the end of the telnet command:
telnet[host/address[port]]
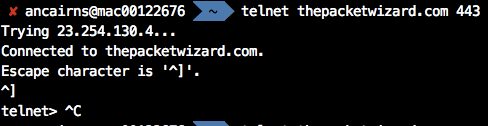
As you can see 443 is open. To exit from the Telnet session:
SHIFT ]
This telnet test to port 23 is not open as it does not say Connected to…
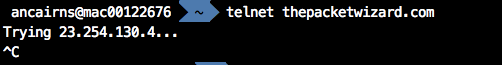
If a remote host does not respond to telnet it can mean a number of things.
- The Firewall or Firewalls or other networking devices on the path to the remote host is Denying or Dropping the packets. You will be able to confirm that in the logs on the firewall.
- The server or remote host on the other side is not up and active
- There is no connectivity to the remote host for some other reason
Further troubleshooting is required if you encounter issues.