Spanning Tree Protocol also known as STP
There are many different types of STP but here are a couple of the main ones
STP/802.1D – Original STP
PVST+ – Cisco Improved STP adding per VLAN feature
RSTP/802.1w – Improved STP with a much faster convergence time (Rapid Spanning Tree)
Rapid PVST+ – Cisco improved RSTP adding per VLAN feature
Why Per VLAN STP?
If you have a large network with lots of switches and VLAN’s you can use Per VLAN STP to plan for a more efficient network
Even although there are many versions of STP they all use a very similar set of rules.
What is STP?
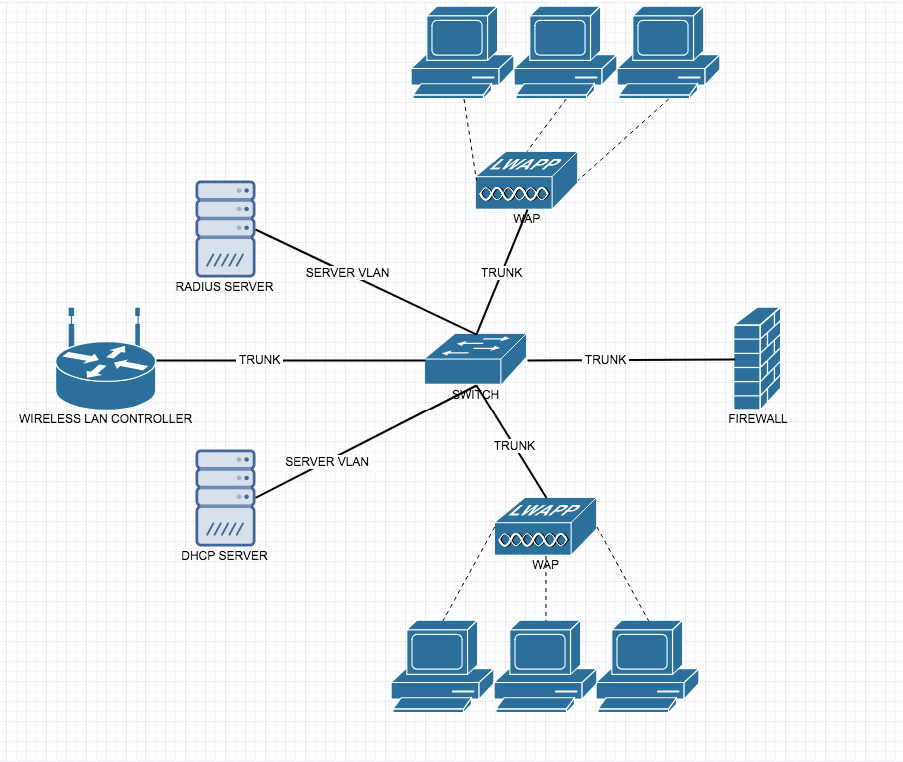
STP is a feature used to prevent loops when you are using redundant switches and without STP a loop could form and cause a number of problems on the network.
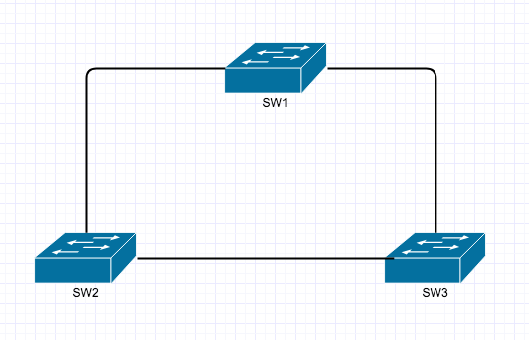
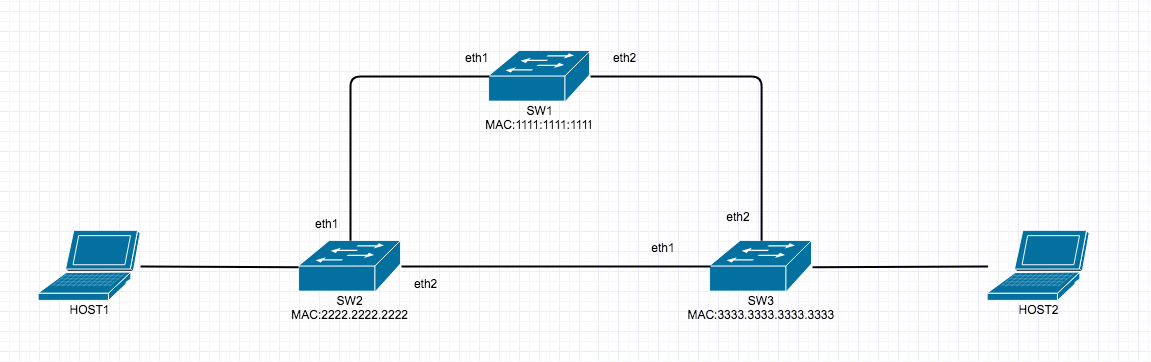
During a unicast broadcast message (which happen all the time) the switch will forward the frame out of every port except the one it came in on. Therefore if SW1 sends a frame out and SW2 and SW3 receive it then SW2 and SW3 will forward out all ports except the one it came in on. SW2 sends to SW3 and SW1. SW3 send to SW2 and SW1 and you can see how the loop is now beginning to form. This is known as a broadcast storm, this can kill a switches CPU and Memory usage very quickly.
The second problem is the MAC address being changed all the time as it receives frames. For example SW1 sends a broadcast message, SW2 and SW3 receive it, then forward it out all other ports like in the scenario above. However each switch learns the MAC address of the next switch and assigns that in the MAC address table, but if you consider SW1 sending to SW2 and SW3 and then SW2 and SW3 forwarding those frames and they eventually get back to SW1 but on different ports, then the MAC Address table will change constantly from I know about SW2 on this port, I now know about SW2 via SW3 on this port, and that can cause unstable MAC address tables.
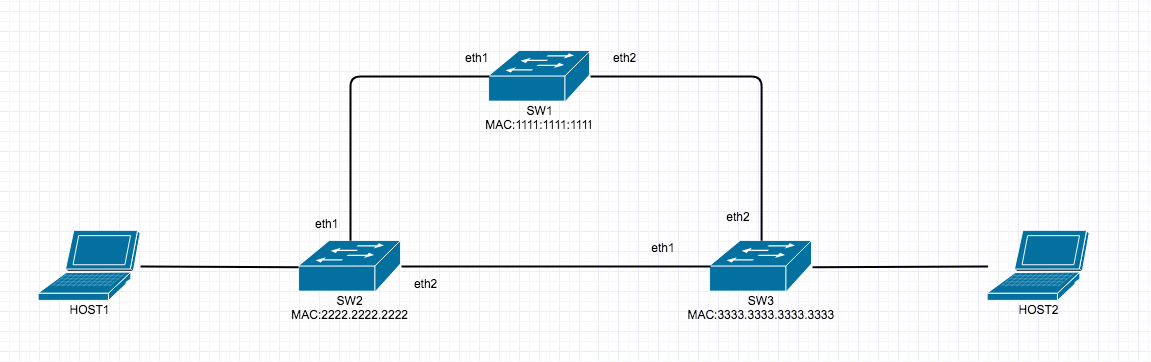
Another issues is explained below
HOST1 sends data to HOST2, however since SW2 doesn’t know how to get to SW2 it sends frames out all ports, thus sending to SW1 and SW3 so HOST2 receives frames from HOST1 via SW3 and then again via SW1>SW3. This is known as Duplicate Frames.
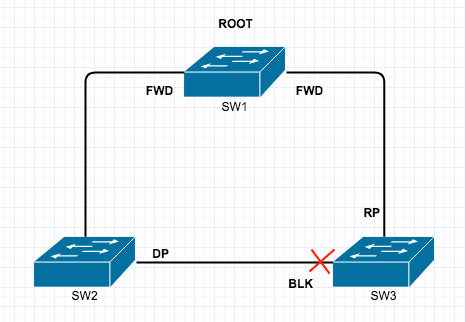
So how do we fix the issues mentioned above? Thats right Spanning Tree Protocol by blocking one of the redundant paths.

The question now becomes how do the switches decide on that Port to block? STP follow’s strict rules, when deciding what ports to block.
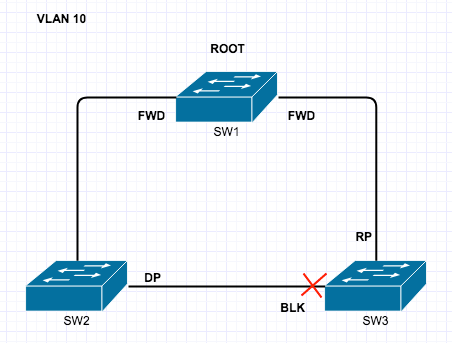
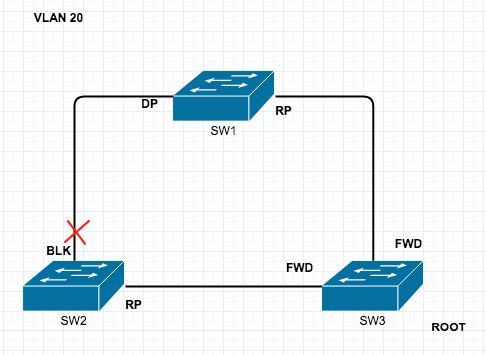
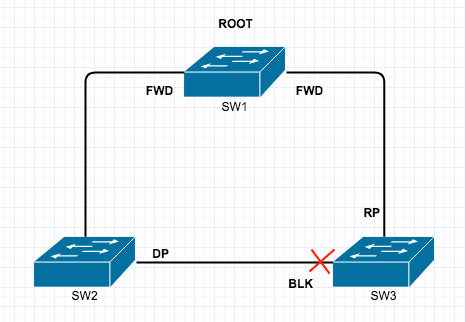
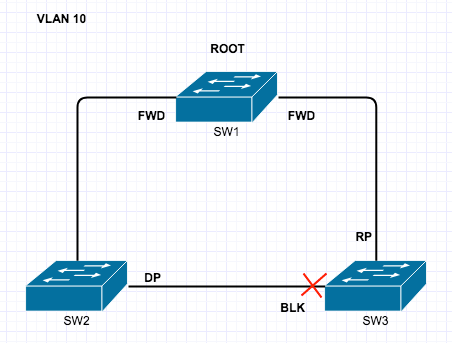
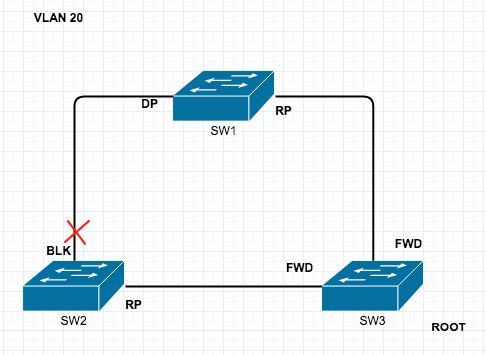
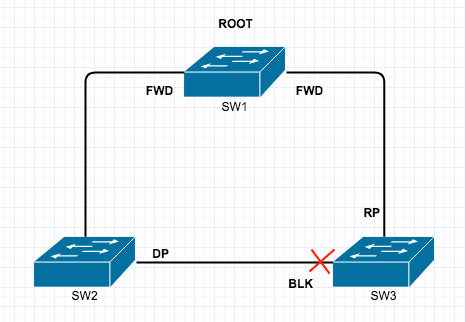
1) Elect a Root Bridge (ROOT)
2) Place root interfaces into forwarding (FWD)
3) Select Root Port on non-Root Bridge Switches (RP) – this is the best root to the Root Bridge.
4) Non Root Switches decide on a Designated Port (DP)
5) All other ports put into Blocking State (BLK)
On per VLAN STP You could have this on VLAN 10
and this on VLAN 20
I will now cover the port roles and the port states so you know what each is:
ROLES
Root Ports : The best port to get to the Root Bridge
Designated Ports : The Lowest cost alternate best root to the Root Bridge.
Non Designated Ports : All other ports that are in blocking mode.
STATES
Disabled : A Port is shutdown
Blocking : A Port that is blocking traffic
Listening : A Port that is not forwarding and not learning MAC addresses
Learning: A Port that is learning MAC addresses but is not forwarding traffic
Forwarding : A Port that is sending and receiving traffic as normal
When ports change from one Role to another it will go through the Port States. Note also that the Listening and Learning states are transitional and it wont stay on either.
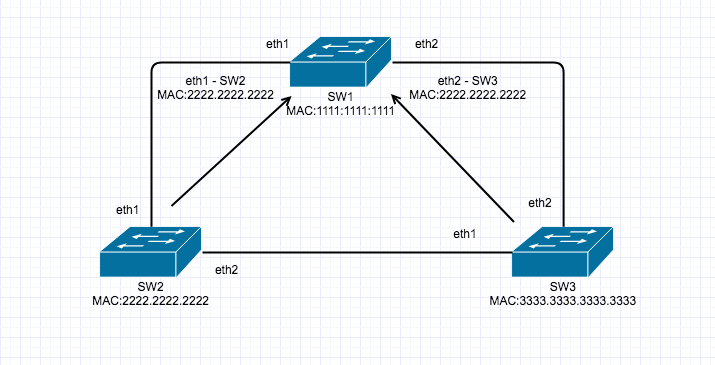
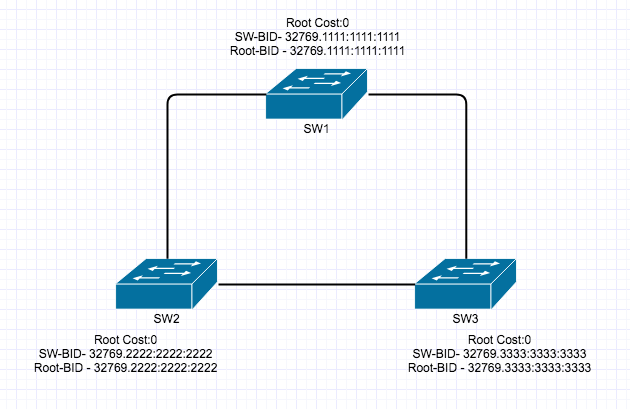
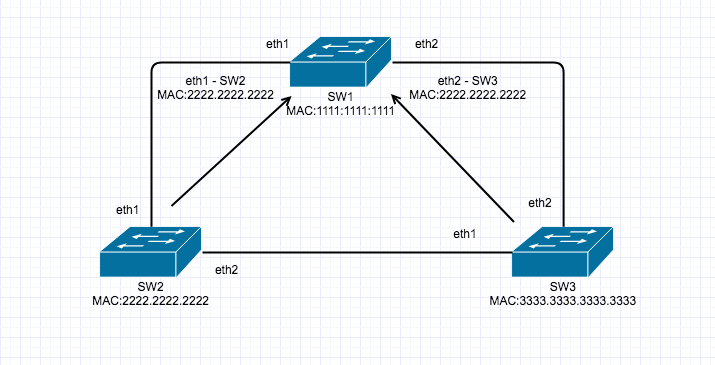
Root Bridge Election
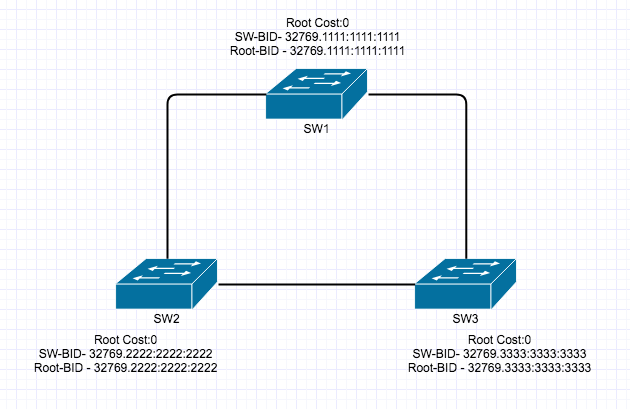
Each switch has and sends messages to each other called Bridge Protocol Data Units (BPDU’s) These BPDU’s contain specific information pertaining to each switch, such as Root Cost, Bridge ID (BID) for Itself and for the Root. A BID is made up of STP Priority and MAC address, the default value of The BID on SW1 would be 327691111:1111:1111 since 32769 is the default STP priority and the MAC address. The switch with the lowest BID will become the Root Bridge. This is what is looks like before the Root Bridge Election and the exchange of the BPDU’s
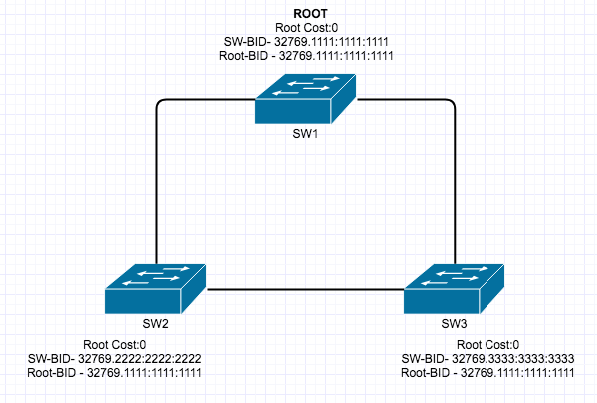
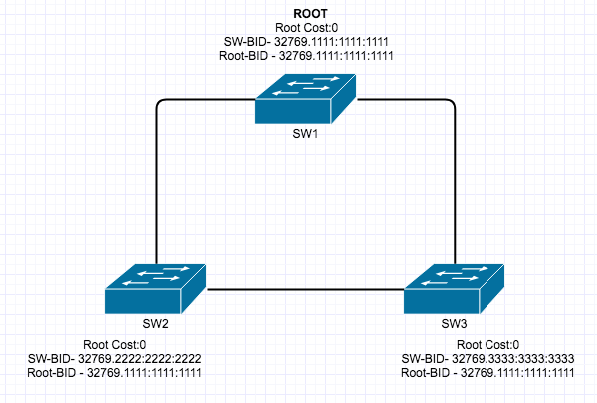
This is what it looks like after, when the lowest BID wins.
The ports on each switch now transition into their respective states following the STP Rules as mentioned above.
The ports can change based on the Cost of each link. The port costs are listed below, however in this example we will just be using Gig Ports, but for clarity a FastEthernet Port will be slower than a GigEthernetPort, the faster the port the lower the cost. The Root Port (RP) is the lowest port cost.
| Data rate |
STP cost |
RSTP cost |
| (Link Bandwidth) |
(802.1D-1998) |
(802.1W-2004, default value) |
| 4 Mbit/s |
250 |
5,000,000 |
| 10 Mbit/s |
100 |
2,000,000 |
| 16 Mbit/s |
62 |
1,250,000 |
| 100 Mbit/s |
19 |
200,000 |
| 1 Gbit/s |
4 |
20,000 |
| 2 Gbit/s |
3 |
10,000 |
| 10 Gbit/s |
2 |
2,000 |
| 100 Gbit/s |
N/A |
200 |
| 1 Tbit/s |
N/A |
20 |
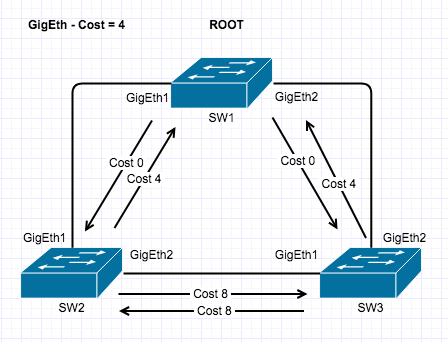
This is a quick diagram of how the port costs are worked out to get back to the Root Bridge. SW2 to get to SW1 is 0+4=4 and SW2 via SW3 to SW1 is 4+4=8
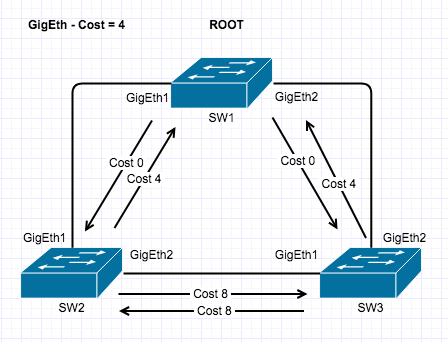
Of course there can be ties between multiple connections and STP can be tuned.
Designated Ports are selected by Root Cost the by Lowest BID and then by lowest numbered Interface. Therefor in the diagram above the Designated port would be GigEth1 on SW3 since it is a lower numbered interface than SW2 GigEth2.
All ports that are not Root Ports or Designated Ports are Blocking Ports.
STP Convergence Times
STP:
BPDU/Hello time = 2 secs – Hello messages to each switch to see its still there
Max Age = 20 secs – How long a switch will wait for a response to the Hello message
Listening = 15 secs
Learning = 15 secs
= 52 secs to convergence
From the time a link goes down to convergence it takes a total of 52 Seconds. When STP was designed that was fine but now, this is much too slow which is where Rapid Spanning Tree Comes in.
RSTP:
3 missed BDPU/Hello at 2 sec each = 6 secs
Learning (no listening) = 15 secs
= 21 secs to convergence.
I hope this have given you a good explanation of STP.