We have been working to migrate off the old Cisco ASA Firewalls for 3 months, we swung over the final VLAN today and turned off the 2nd of 3 Cisco ASA’s. Huge Achievement!!! Two more to go. Here is a video of me doing the honor.
Turning off Cisco ASA Firewall
We have been working to migrate off the old Cisco ASA Firewalls for 3 months, we swung over the final VLAN today and turned off the 1st of 3 Cisco ASA’s. Huge Achievement!!! Two more to go. Here is a video of my colleague Tom doing the honor of turning it off.
Network Utilities : SuperPutty Setup
I only use SuperPutty with GNS3, here is how.
- GNS3 as of 1.5.2 doesn’t include the latest version so download it from here:
- Start SuperPutty which will present you with the configuration options. Set the following:
- YOU MUST USE THE PUTTY PROVIDED WITH GNS3. If you don’t, you’ll receive errors “unknown option -wt” when opening consoles with SuperPutty from GNS3
- putty.exe location (Required): C:\Program Files\GNS3\putty.exe
- Or where-ever GNS3 is installed
- Click the “Advanced: tab > Check off “Only allow single instance of SuperPutty to run”
- Set the other options however you like
- Open up Preferences in GNS3 > General > Console applications tab
- Change the console application for telnet and serial to use SuperPutty
- If you want to use keep the same color scheme that is used by the regular Putty console, add “-gns3 5 -skin 4” at the end i.e.
- c:\dropbox\apps\superputty\SuperPutty.exe -telnet “%h -P %p -wt \”%d\” -gns3 5 -skin 4″
GNS3 : Install and Configure
This install is intended for running IOU/IOL images on the GNS3 VM because it is the preferable way of running IOS in GNS3 now.
Pre-Requisites:
- Install VMware Workstation Player
http://www.vmware.com/products/player/playerpro-evaluation.html - Install VMware VIX API
https://www.vmware.com/support/developer/vix-api/ - Install Wireshark
https://www.wireshark.org/download.html
Install WinPCAP provided by Wireshark
Install GNS3:
- Install GNS3
https://www.gns3.com/software/download - Install only the following components:
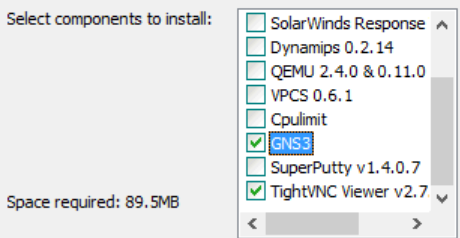
- We don’t need Dynamips/QEMU/VPCS/Cpulimit because we’ll be running everything off of the GNS3 VM server. We don’t install SuperPutty from here because its not the latest version and the first thing it does when you open it is bug you about upgrading to the latest version. There are setup instructions for it below.
Install Loopback Adapter
- Open an Admin Command Prompt
cd “c:\Program Files\gns3”
loopback-manager.cmd
- Install a new Loopback interface (reboot required)
- Reboot
- Rename the new Loopback adapter to “Loopback”
- Assign it an IP address
Setup GNS3 VM:
- Download the GNS3 VM version that matches the installed GNS3 version
https://github.com/GNS3/gns3-gui/releases - Import the VM and keep the defaults
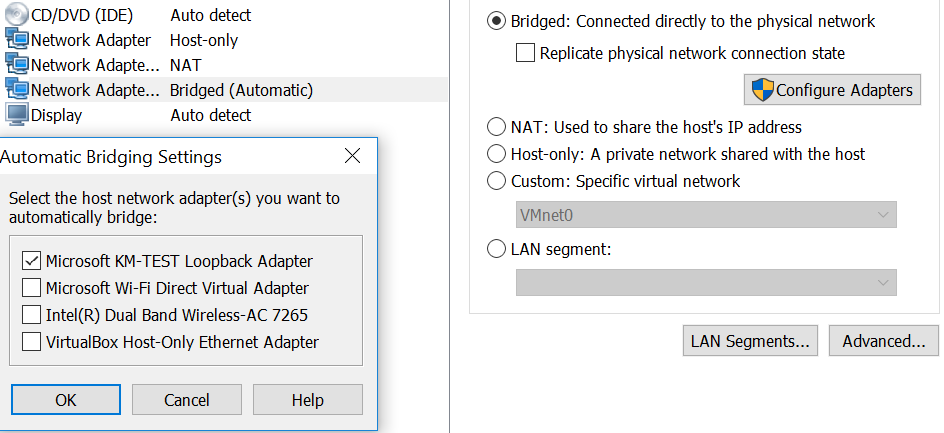
- Add a 3rd Network Adapter that will be in Bridged mode and connected to the Loopback adapter (Microsoft KM-TEST Loopback Adapter)
- Power on the VM
- SSH into the VM using gns3/gns3 for the credentials
- Sudo to root and run the following:
- echo ‘127.0.0.127 xml.cisco.com’ >> /etc/hosts
- Sudo to root and run the following:
- Leave the VM powered on, we’re done with it for now
- Open an Administrator command prompt
- cd into the GNS3 install directory and run the following:
- IMPORTANT: On my work laptop, added the additional interfaces broke network connectivity to the VM after they were added. I have no idea why but after I reinstalled VMware Workstation which uninstalled all the adapters, I was able to connect to the VM again. On the work laptop, I’m running without the additional adapters and it seems fine so far.
- vmnet-manager.cmd
- Select option 1 which will add the vmnet interface 2 to 19 (this can take a while, please be patient)
- If it looks like this process has hung, you follow step 2 in the url below to add the adapters
https://www.gns3.com/support/docs/how-to-use-vmware-player-in-gns3
Configure GNS3 to use the GNS3 VM server:
- Open up GNS3
- Goto Edit > Preferences
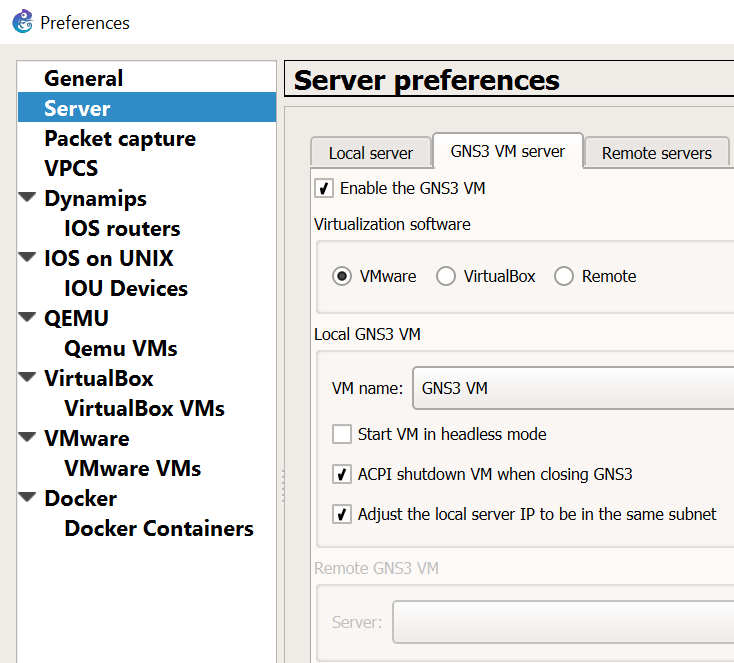
Be sure to leave “Start VM in headless mode” unchecked. I ran into issues where the VM would not automatically startup when opening GNS3 and also cause the GNS3 process to linger when closing out of it. -
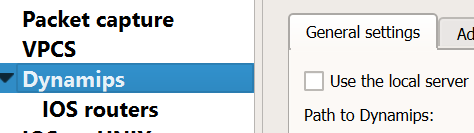
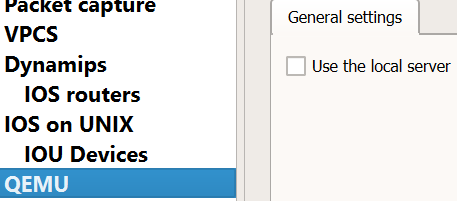
Disable “Use of the local server” for Dynamips and QEMU. We’ll use the GNS3 VM instead for running those processes.

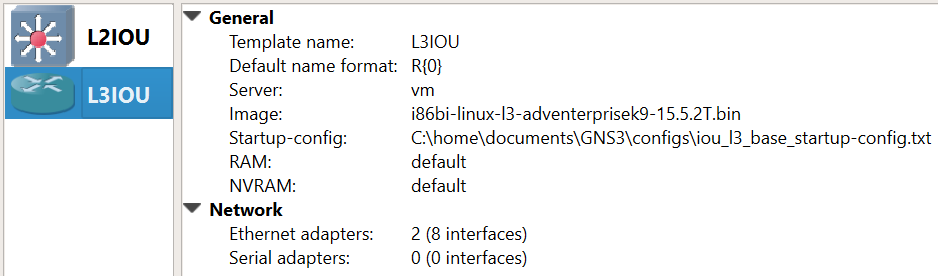
Create the L2/L3 IOU Devices:
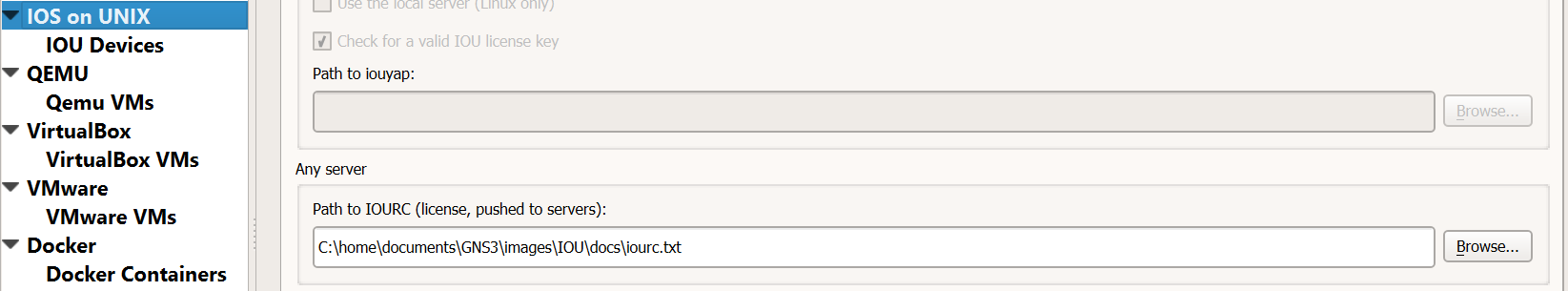
- Goto Edit > Preferences
- Set the iourc file to use with the license (IOU devices need a license to run)
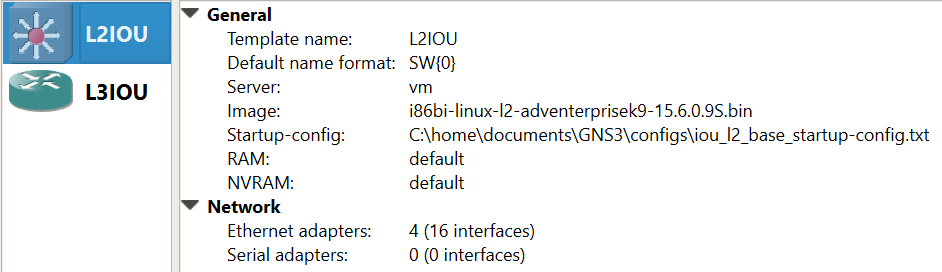
- Create the L2 image:
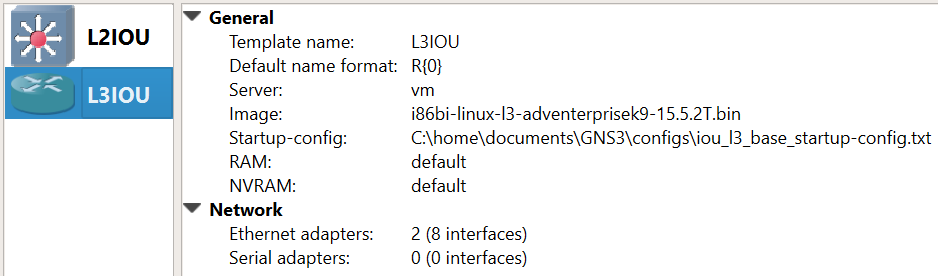
- Create the L3 image:
Add Device Image
New appliance template > Add and IOU > Run the IOU > New Image > Browse
i86bi-linux-l2-ipbasek9-15.1e.bin – IOU-L2
i86bi-linux-l3-adventerprisek9-15.4.2T.bin – IOU-L3
Operational Notes:
- Sometimes a restart of all the routers/switches are required when new links are created between devices. Even though the line protocols show as up, I’ve found a restart is required for traffic to actually pass through them.
If you want to use SuperPutty as the SSH client for GNS3 click this link:
SuperPutty with GNS3
The Packet Wizard : First Ever Fan Mail
Yesterday I received my first ever fan mail. I am grateful the blog is proving useful to some, and as my content grows hopefully the usefulness of the blog also grows. If anyone want to send me mail or anything else I am open to that. I accept : IOU’s, Gift Cards, Cash, Precious Gems, Hugs, and IT equipment. In all honesty I am over the moon its helping someone.
Cisco : Serial Numbers
Today I have spent some time trying to find serial numbers on multiple Cisco devices, some Routers, Switches, Firewalls and Wireless LAN Controllers. Here is 7 ways I have found:
- Locate the serial number tag on the device chassis.
- The serial number is displayed in the banner during boot.
- “show version” command. (Look for Processor board ID or S/N)
- “show inventory” command. (Look for Hw Serial# or SN:)(Also works on WLC’s)
- “show diag” command. (Look for Chassis Serial Number)
- “show hardware” command. (Look for Processor board ID or S/N)
- “show tech-support” command.
SecureCRT : Logging
Logging your session when doing any kind of network work is very important and can save your ass. It has saved mines on multiple occasions. One reason is it allows you to look back and see what you may have done wrong, so you can troubleshoot a issue more effectively. Other reasons are it give you the user a quick way to backup a device if you show the configuration file when working on it. I make it a habit of showing the configuration file before I do any work, so I always have a back out strategy incase something goes wrong.
SecureCRT Logging
Options > Edit Session Defaults
File path to where you are storing your logs /Logs/%M-%D-%Y/%S (%H) — %h-%m.log
Start Log Upon Connect
Append to File
Start recording S (%H) – %h:%m:%s
Stop recording S (%H) – %h:%m:%s
Happy Logging!
Cisco/Brocade : Basic Similar Commands
- Here are some basic switch commands and the Cisco to Brocade differences, even though the OS’s are similar they have some subtle differences.
|
Task |
Cisco |
Brocade |
|
Configure a VLAN |
Interface vlan 2 |
Vlan 2 |
|
Configure a trunk port |
Int fa0/1 Switchport trunk encap dot1q Switchport mode trunk |
Vlan 2 Tagged eth 0/1/1 Vlan 3 Tagged eth 0/1/1 Vlan 4 Tagged eth 0/1/1 Interface ethernet 0/1/1 Dual-mode 1 |
|
Configure a access port |
Int fa0/1 Switchport access vlan 2 |
Vlan 2 Untagged eth 0/0/1
|
|
Configure an IP address on a VLAN |
Int vlan2 Ip address 192.168.1.1 255.255.255.0 |
Vlan 2 Router interface ve 1 Interface ve1 Ip address 192.168.1.1 255.255.255.0 |
|
Configure a range of ports |
Int range fa0/1-10 |
Int eth 0/1/1 to 0/1/5 |
|
Configure a port for both voice and data vlans |
Int fa0/1 Switchport access vlan2 Switchport voice vlan3 |
vlan2 Tagged eth 0/1/1 vlan3 Tagged eth 0/1/1 Inter eth 0/1/1 Dual-mode 1 Voice-vlan 3 Inline power |
|
Show the interface status of a port/vlan |
Sh int fa0/1 |
Show int eth 0/1/1 |
|
See CDP Neighbors |
Show cdp neighbors |
Show fdp neighbors |
The Packet Wizard : Update May 11th 2017
Since I started this blog a few weeks ago, I have not been able to post once per week as I would have liked, there have been a number of reasons, mostly though, time.
I have been working like a maniac at work and learning a bunch of new stuff, which in turn will provide some awesome blog material. I hope to finish up writing these in the next week or so between work travel to Montreal, A full week of Palo Alto Firewall Training and another 2 week work trip to Australia.
Upcoming blog material will include : Palo Alto and Amazon Web Services AWS (which I spent 2 weeks working on and configuring). All very fascinating stuff.
Brocade : SSH Setup
Delete Crypto Key
Conf t
Crypto key zeroize
Generate Key Pair
Conf t
Crypto key generate <CR> – will create a DSA Key pair
crypto key generate rsa modulus 2048 – 2048 RSA Key
Create Local Username and Password
Username nocadmin password <password>
Enable AAA
Aaa authentication login default local
Verify
Show who – shows SSH connections

